1. Introduction
The global deployment of the (5G) wireless networks has transformed the telecommunication landscape. With the introduction of ultra-low latency, massive device density, and very high bandwidth, the 5G represents an architectural shift in the telecom network design not just an upgrade from the 4G.
The new capabilities enables innovations across different industries like autonomous transportation, IoT, telemedicine, smart cities, and defence communications.
However, this advancement comes with a significant challenge:
5G dramatically expands the cybersecurity attack surface due to its software-driven design and huge connectivity requirements.
The previous telecom network relied heavily on centralised, hardware-based systems, but 5G is built on virtualisation, programmability, cloud-native functions, and distributed architecture. This makes 5G more flexible-but also more vulnerable to emerging cyber threat.
This article provides a technical overview of why 5G cybersecurity is now a critical priority.
2. 5G Introduces a New Cyber Risk Model
2.1 From Hardware-Centric to Software-Defined Architecture
In 3G and 4G networks, the core functions implementation were based on a dedicated hardware appliances. The security controls were centralised and fixed. 5G changed that model.
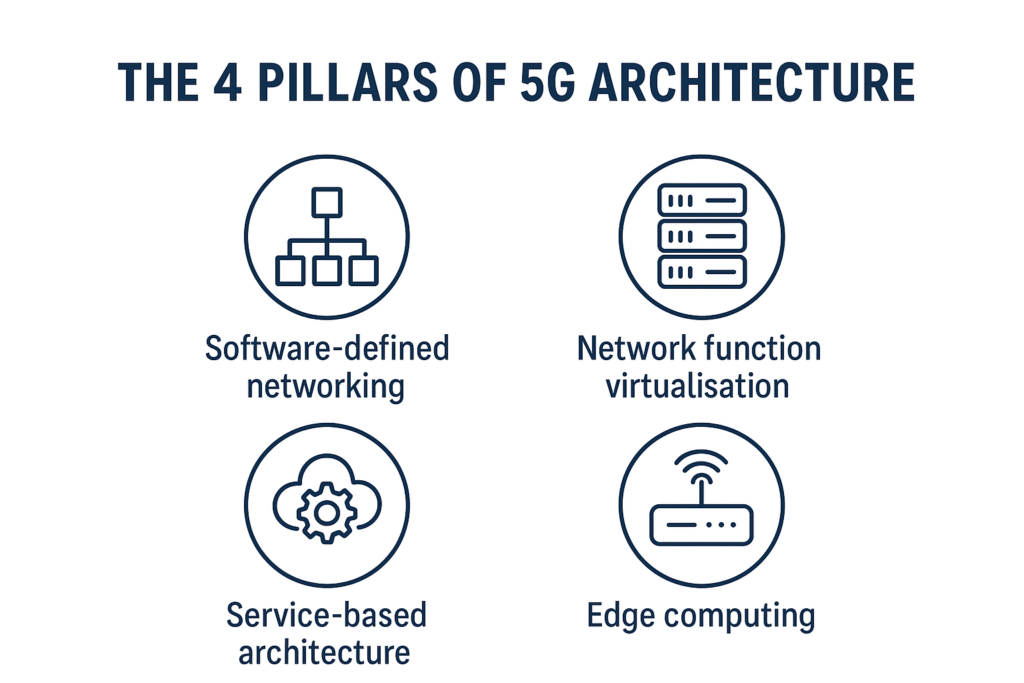
5G relies on:
- Software Defined Networking (SDN) for the programable control plane management
- Network Function Virtualisation (NFV) to replace the hardware with virtual network functions
- Service-based Architecture (SBA) built on APIs
- Cloud-native 5G Core (Containers, orchestration, CI/CD pipelines)
- Distributed edge computing
Although the new capabilities the 5G has, these also introduce:
- More attack vectors
- More opportunities for lateral movement
- new vulnerabilities inherited from cloud-native systems
- The multi-vendor deployment introduce supply chain risks
As Alnaim (2024) highlighted, the traditional perimeter-based security models do not apply to a software-driven 5G core.
3. Massive Expansion of the Attack Surface
3.1 IoT and Device Density
5G networks are used to support up to million devices per square kilometre. These devices:
- Have limited processing power
- Have weak or no authentication
- Hardly receive firmware updates
- Deployed at massive scale
- Are easily compromised
This makes IoT devices ideal for botnets and distributed attacks.
A systematic review by Gelgi et al. (2024) shows that IoT botnets are one of the fastest growing global cyber threats.
3.2 Multi-Tenant Architecture Increases Complexity
The 5G network slicing feature enables the operators to create multiple virtual networks on a shared infrastructure. The slice security relays on the proper configuration of the slice.
Research by Aguilar-Mora & Merino-Vivanco (2025) shows that slice misconfiguration could cause:
- Lateral movement between the slices
- Cross-tenant Data leakage
- Escalating attacks from low-critical to high-critical slices
This is an introduction of new risks that did not exist before in the previous generations.
3.3 Distributed Edge Computing Expands Vulnerabilities
In 5G, the compute and storage are moved to the edge to support the ultra-low latency. But this distribution make each site:
- An entry point
- A target
- A new attack surface
In the traditional security models which include (Central firewalls, Perimeter DMZs) are not effective in the 5G decentralised network architecture.
4. Protocol-Level Weaknesses Still Exist
The 5G improved LTE protocols, however vulnerabilities still exist:
- IMSI catching still possible with downgrade conditions
- Traceability attacks can reveal the subscriber pattern of movement
- Downgrade attacks forcing 5G devices to fall back to 4G and 3G
Research by Piqueras Jover & Marojevic (2018) shows that attackers can exploit the 5G signalling weaknesses using rogue base stations and protocol manipulation.
5. The Shift Toward Cloud-Native 5G Security
The 5G core networks run on containerised environments (e.g., Kubernetes) which introduces security risks:
- Insecure container images
- Exposed APIs
- Orchestrators misconfiguration
- Weak CI/CD pipelines
- Privilege escalation between services
The Cloud Security Alliance (2025) highlights that Zero Trust Architecture (ZTA) is essential for securing the Kubernetes-based 5Gcore functions.
6. The Need for New Security Models
The 5G requires the shift from “trust by default” to:
- Zero trust
- Continuous authentication
- Micro-segmentation
- Identity-centric security
- Behaviour-based AI detection
- Secure-by-design orchestration
There is a challenge as threats evolve rapidly in the programmability environments that the traditional static security controls cannot keep pace.
7. Conclusion
5G is not just a faster generation, it is a new architecture with new risks.
With the combination of:
- Virtualised core
- Massive IoT density
- Multi-tenant slicing
- Edge computing
- Cloud-native functions
The 5G creates a dynamic, high-risk environment that needs a dynamic cybersecurity approach.
This article sets the foundation for the next blogs that will explore:
- Network slicing vulnerabilities
- Protocol-level threats
- AI/ML security
- Zero Trust architectures
- Blockchain for identity
- 5G global regulatory
8. References
Aguilar-Mora, C.D., Merino-Vivanco, R.P. (2025). Security Considerations for 5G Network Slicing. In: Marreiros, G., et al. Distributed Computing and Artificial Intelligence, Special Sessions II, 21st International Conference. DCAI 2024. Lecture Notes in Networks and Systems, vol 1151. Springer, Cham. https://doi.org/10.1007/978-3-031-80946-0_34
Alnaim, A. K. (2024). Securing 5G virtual networks: A critical analysis of SDN, NFV, and network slicing security. International Journal of Information Security, 23(6), 3569–3589. https://doi.org/10.1007/s10207-024-00900-5
Cloud Security Alliance. (2025, July 14). Zero trust lessons from a real-world 5G cloud core security assessment. CSA Blog. Retrieved from Cloud Security Alliance website https://cloudsecurityalliance.org/blog/2025/07/14/zero-trust-lessons-from-a-real-world-5g-cloud-core-security-assessment
Gelgi, M., Guan, Y., Arunachala, S., Samba Siva Rao, M., & Dragoni, N. (2024). Systematic literature review of IoT botnet DDoS attacks and evaluation of detection techniques. Sensors, 24(11), Article 3571. https://doi.org/10.3390/s24113571
Piqueras Jover, R., & Marojevic, V. (2018). Security and protocol exploit analysis of the 5G specifications. arXiv preprint arXiv:1809.06925. https://arxiv.org/abs/1809.06925
